Cybersecurity revenge porn prevention requires a multi-layered approach combining legal protections, technical security measures, and proactive digital safety strategies. Non-consensual image sharing, commonly known as revenge porn, affects millions globally with devastating personal and professional consequences. This comprehensive guide explores evidence-based legal frameworks, advanced technical prevention methods, and practical cybersecurity measures to protect against unauthorized intimate image distribution in 2026.
What Is Revenge Porn and Why Is Cybersecurity Prevention Critical?
Revenge porn refers to the distribution of sexually explicit images or videos without the consent of the individuals depicted. This form of image-based sexual abuse has evolved into a sophisticated cybersecurity threat requiring comprehensive prevention strategies.
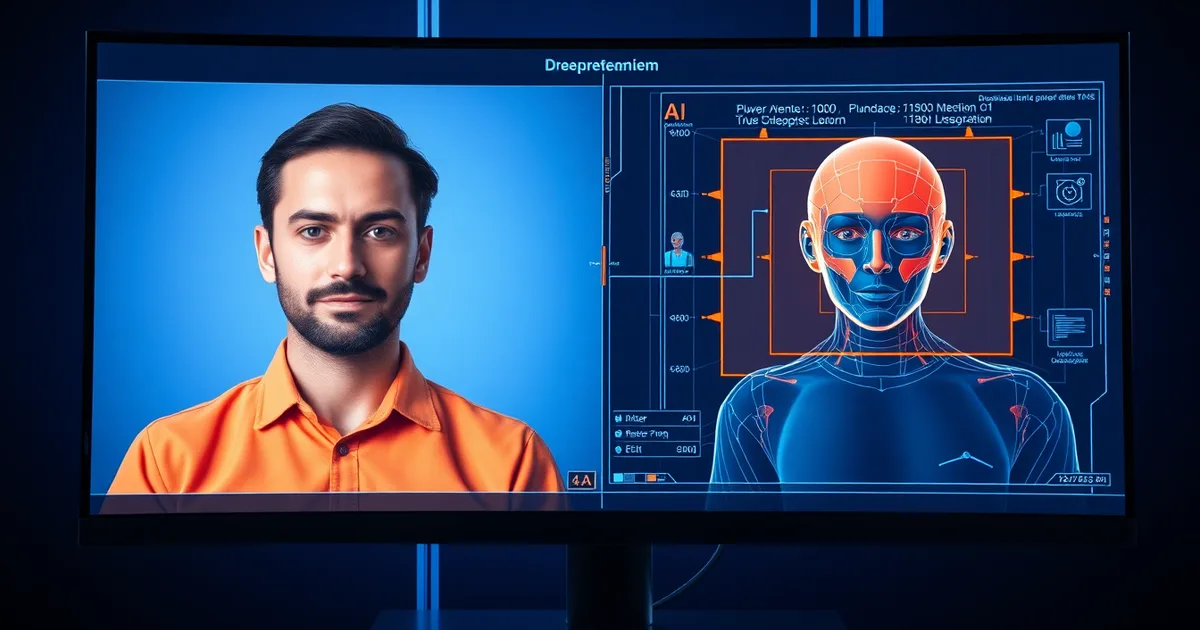
The digital landscape in 2026 presents unique challenges for cybersecurity revenge porn prevention. Advanced AI technologies can now create deepfake intimate images, while social media platforms and messaging apps provide multiple vectors for non-consensual sharing.
According to recent cybersecurity research, over 4.5 million people have experienced threats of non-consensual image sharing, with women comprising 75% of victims. The financial impact averages $8,000 per victim in legal fees, therapy costs, and lost employment opportunities.
Understanding the intersection of social media stalking protection and revenge porn prevention is crucial for comprehensive digital safety strategies.
How Do Legal Frameworks Protect Against Non-Consensual Image Sharing?
Legal protections against revenge porn have significantly strengthened since 2024, with comprehensive legislation now covering both traditional and AI-generated intimate images across most jurisdictions.
Federal and International Legal Protections
The United States implemented the SHIELD Act in 2025, criminalizing non-consensual intimate image sharing at the federal level. This legislation includes provisions for AI-generated content and cross-border enforcement mechanisms.
Key legal protections include:
- Criminal penalties: Up to 5 years imprisonment for first-time offenders
- Civil remedies: Statutory damages of $10,000-$150,000 per violation
- Platform liability: Social media companies face penalties for failing to remove content within 48 hours
- International cooperation: Bilateral agreements for cross-border enforcement
State-Level Legislation Variations
All 50 US states now have revenge porn statutes, with varying definitions and penalties. California's updated law includes the broadest protections, covering AI-generated images and requiring platform compliance audits.
European Union's Digital Services Act 2026 mandates immediate takedown procedures and requires platforms to implement proactive detection systems for non-consensual intimate content.
What Technical Security Measures Prevent Unauthorized Image Access?
Technical cybersecurity revenge porn prevention focuses on securing devices, communications, and storage systems to prevent unauthorized access to intimate content.
Device Security Fundamentals
Implementing robust device security forms the foundation of technical prevention strategies:
- Multi-factor authentication: Enable on all devices and cloud storage accounts
- Biometric locks: Use fingerprint, face, or iris recognition for device access
- Encrypted storage: Store sensitive content in password-protected, encrypted folders
- Regular security updates: Maintain current operating systems and security patches
- App permissions audit: Regularly review and restrict application access to cameras and storage
Advanced Digital Protection Technologies
Emerging technologies in 2026 provide sophisticated protection mechanisms:
- Content authentication: Blockchain-based image verification systems
- Watermarking technology: Invisible digital signatures tracking image origins
- AI detection tools: Automated systems identifying potential non-consensual sharing
- Secure communication protocols: End-to-end encrypted messaging with disappearing media
Understanding password manager security strategies is essential for protecting accounts that may contain sensitive information.
How Can Individuals Implement Proactive Prevention Strategies?
Proactive cybersecurity revenge porn prevention requires individuals to adopt comprehensive digital hygiene practices and utilize available protection tools.
Personal Digital Security Audit
Conducting regular security audits helps identify vulnerabilities before they can be exploited:
- Inventory sensitive content: Catalog all intimate images across devices and platforms
- Assess sharing history: Review past sharing patterns and recipient trustworthiness
- Evaluate platform security: Audit privacy settings on all social media and cloud storage accounts
- Check data breaches: Monitor for account compromises using breach notification services
- Review relationship digital footprints: Assess potential risks from current and former partners
Secure Content Creation and Sharing Practices
Implementing secure practices during content creation minimizes long-term risks:
- Avoid identifiable features: Exclude faces, tattoos, or distinctive backgrounds
- Use secure platforms: Choose messaging apps with strong encryption and deletion features
- Implement time limits: Utilize disappearing message features for sensitive content
- Create sharing agreements: Establish explicit consent protocols with partners
- Regular content purges: Periodically delete sensitive content from all devices
What Role Do Technology Platforms Play in Prevention?
Technology platforms bear significant responsibility for cybersecurity revenge porn prevention through policy enforcement, detection systems, and user protection tools.
Platform Detection and Removal Systems
Major platforms have implemented sophisticated detection systems by 2026:
- PhotoDNA technology: Hash-based image matching across platforms
- AI content analysis: Machine learning systems detecting non-consensual intimate content
- User reporting mechanisms: Streamlined processes for content removal requests
- Proactive monitoring: Automated scanning for policy violations
- Cross-platform cooperation: Shared databases preventing re-uploads
User Protection Features
Platforms now offer comprehensive protection tools:
| Platform Feature | Protection Level | Implementation Status |
|---|---|---|
| Image hashing | High | Universal across major platforms |
| Takedown automation | Medium-High | 85% of platforms |
| User blocking tools | Medium | 95% of platforms |
| Content warnings | Medium | 70% of platforms |
| Legal reporting assistance | High | 60% of platforms |
How Should Victims Respond to Non-Consensual Image Sharing?
Immediate response protocols can minimize damage and preserve evidence for legal proceedings when cybersecurity revenge porn prevention fails.
Immediate Response Steps
Time-sensitive actions maximize chances of successful content removal:
- Document everything: Screenshot evidence before content is removed or modified
- Report to platforms: Submit takedown requests through official channels
- Contact law enforcement: File reports with local police and relevant federal agencies
- Secure additional accounts: Change passwords and enable additional security measures
- Notify trusted contacts: Alert employers, family members, and close contacts proactively
Legal Remedies and Support Resources
Comprehensive support systems exist for victims of non-consensual image sharing:
- Legal aid organizations: Free consultation and representation services
- Victim advocacy groups: Emotional support and practical assistance
- Professional counseling: Specialized therapy for image-based sexual abuse
- Financial assistance programs: Grants covering legal fees and security measures
- Career protection services: Professional reputation management assistance
Understanding digital aftercare strategies can help victims rebuild their online presence safely.
What Are Emerging Threats in Non-Consensual Image Sharing?
The threat landscape for cybersecurity revenge porn prevention continues evolving with advancing technology and changing social media practices.
AI-Generated Content Threats
Deepfake technology poses unprecedented challenges for cybersecurity revenge porn prevention. Sophisticated AI can now create convincing intimate images using only publicly available photos.
Key emerging threats include:
- Deepfake applications: Consumer-grade software creating realistic fake intimate content
- Voice synthesis: AI-generated audio accompanying manipulated images
- Video deepfakes: Moving image manipulation becoming more accessible
- Mass generation attacks: Automated creation of fake content targeting multiple victims
New Distribution Channels
Evolving social media platforms and communication technologies create new vectors for non-consensual sharing:
- Decentralized platforms: Blockchain-based networks resistant to traditional takedown methods
- Encrypted messaging apps: Private group sharing circumventing platform policies
- Gaming platforms: Image sharing within online gaming communities
- Professional networks: Workplace harassment through business-focused platforms
How Do Educational Institutions Address Prevention?
Educational approaches to cybersecurity revenge porn prevention focus on digital citizenship, consent education, and bystander intervention training.
Comprehensive Digital Citizenship Programs
Schools and universities now implement mandatory curricula covering:
- Digital consent education: Understanding legal and ethical boundaries
- Cybersecurity fundamentals: Technical protection measures and best practices
- Bystander intervention: Empowering witnesses to prevent and report violations
- Legal literacy: Understanding consequences and reporting procedures
- Support resource awareness: Connecting students with appropriate help services
Institutional Policy Development
Educational institutions have strengthened policies addressing non-consensual image sharing:
- Clear disciplinary procedures: Defined consequences for policy violations
- Victim support protocols: Comprehensive assistance programs for affected students
- Campus security integration: Coordination with law enforcement when appropriate
- Technology tool provision: Access to security software and monitoring systems
Many institutions now integrate dating app privacy protection into their digital safety curricula.
Practical Prevention Implementation Strategies
Implementing effective cybersecurity revenge porn prevention requires systematic approach combining technical, legal, and behavioral strategies:
- Establish device security protocols: Enable multi-factor authentication, biometric locks, and regular security updates across all devices
- Implement secure content practices: Use encrypted storage, disappearing messages, and avoid identifiable features in sensitive content
- Maintain digital hygiene: Regularly audit platform privacy settings, purge sensitive content, and monitor for security breaches
- Create legal documentation: Establish clear consent agreements and maintain records of authorized sharing
- Build support networks: Connect with advocacy organizations and legal resources before incidents occur
- Stay informed about emerging threats: Monitor developments in deepfake technology and new distribution platforms
- Develop incident response plans: Prepare step-by-step procedures for immediate action if prevention fails
- Invest in professional monitoring services: Consider reputation monitoring and takedown assistance services
- Educate personal networks: Share prevention knowledge with family, friends, and romantic partners
- Advocate for stronger protections: Support legislation and platform policies enhancing victim protections
Technology Tools and Service Comparison
Selecting appropriate cybersecurity revenge porn prevention tools requires understanding available options and their effectiveness levels:
| Tool Category | Example Services | Protection Level | Cost Range | Ease of Use |
|---|---|---|---|---|
| Monitoring Services | Reputation.com, BrandYourself | High | $200-500/month | Medium |
| Takedown Services | CyberCivil Rights, CCRI | High | $1000-5000/incident | High |
| Secure Storage | Signal Private Messenger, ProtonDrive | Medium-High | Free-$10/month | High |
| Device Security | Norton Mobile, Malwarebytes | Medium | $50-150/year | High |
| Legal Insurance | LegalShield, ARAG | Medium | $25-50/month | Medium |
Understanding how these tools integrate with broader cybersecurity protection strategies enhances overall digital safety.
Conclusion
Effective cybersecurity revenge porn prevention in 2026 requires comprehensive strategies combining strengthened legal frameworks, advanced technical security measures, and proactive personal protection practices. The evolving threat landscape, particularly AI-generated content and decentralized distribution channels, demands continuous adaptation of prevention strategies.
Success depends on multi-stakeholder cooperation between individuals, technology platforms, educational institutions, and legal systems. By implementing systematic prevention measures, staying informed about emerging threats, and building strong support networks, individuals can significantly reduce their risk of becoming victims of non-consensual image sharing.
The investment in prevention – both financial and behavioral – far outweighs the devastating personal, professional, and financial consequences of revenge porn victimization. As technology continues evolving, maintaining vigilant cybersecurity practices and advocating for stronger protections remains essential for digital safety and personal autonomy.