Cybersecurity dating app privacy has become a critical concern as millions of users share intimate personal details on dating platforms daily. This comprehensive guide provides essential strategies for protecting your personal data, understanding privacy risks, and implementing robust security measures while navigating the modern online dating landscape. From encryption protocols to profile optimization, learn how to maintain digital safety without compromising your chances of meaningful connections.
What Are the Major Cybersecurity Risks on Dating Apps in 2026?
Dating applications present unique cybersecurity challenges that extend far beyond traditional social media risks. Personal data exposure occurs through multiple vectors, including profile information, messaging content, location data, and behavioral patterns that dating platforms collect and potentially share with third parties.
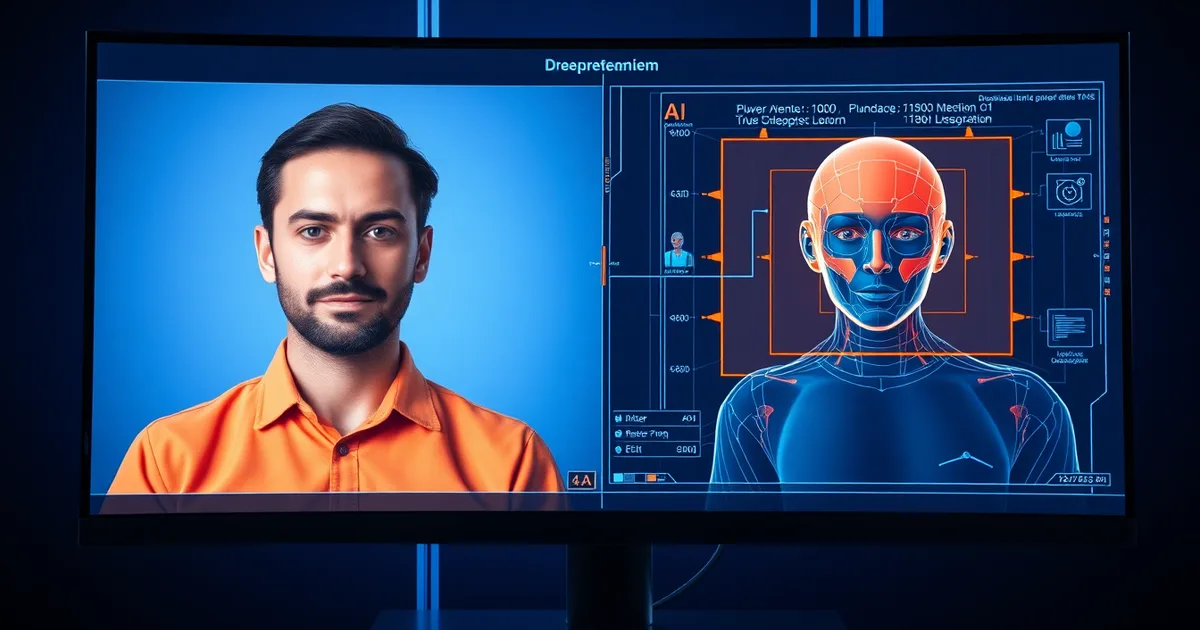
The most significant risks include catfishing attacks, where malicious actors create fake profiles to extract personal information or financial resources from unsuspecting users. Additionally, data breaches have affected major dating platforms, exposing millions of user profiles, private messages, and sensitive personal details to cybercriminals.
Romance scams have evolved into sophisticated social engineering attacks, with criminals using AI chatbots to simulate authentic conversations and build emotional connections before exploiting victims financially. Location tracking vulnerabilities also pose significant risks, potentially enabling stalking or physical harm.
How Do Dating Apps Collect and Use Your Personal Data?
Dating platforms operate complex data collection ecosystems that gather information through multiple channels simultaneously. Primary data collection includes profile information, photos, preferences, and explicit user inputs, while secondary collection involves browsing patterns, app usage duration, swipe behaviors, and message response times.
Behavioral analytics track your interaction patterns, including which profiles you view longest, conversation starters that generate responses, and optimal activity times. This data feeds algorithmic matching systems but also creates detailed psychological profiles that may be shared with advertising networks or sold to data brokers.
Many dating apps integrate with social media platforms, automatically importing contacts, interests, and relationship history. Cross-platform data sharing amplifies privacy risks by creating comprehensive digital footprints that extend far beyond the dating app ecosystem itself.
Essential Data Types Dating Apps Collect
- Identity Information: Name, age, education, occupation, photos
- Behavioral Data: Swipe patterns, message frequency, profile views
- Location Data: GPS coordinates, travel patterns, venue check-ins
- Device Information: Hardware specs, operating system, installed apps
- Communication Content: Messages, voice notes, video calls
- Social Connections: Contacts, social media friends, mutual connections
- Preference Data: Dating criteria, lifestyle choices, relationship goals
Which Dating App Privacy Settings Should You Configure First?
Implementing proper privacy configurations requires systematic attention to multiple security layers within dating applications. Begin by reviewing and restricting data sharing permissions, particularly location access, contact synchronization, and social media integration features.
Location privacy deserves immediate attention, as precise GPS data can enable stalking or unwanted contact. Configure location sharing to show approximate areas rather than exact coordinates, and disable automatic location updates that broadcast your real-time movements to potential matches.
Message encryption settings vary significantly between platforms, with some offering end-to-end encryption while others store conversations on company servers indefinitely. Review data retention policies and enable automatic message deletion where available to minimize long-term privacy exposure.
Critical Privacy Settings Checklist
- Disable precise location tracking - Use approximate location only
- Restrict contact access - Prevent automatic contact importing
- Configure photo permissions - Limit camera and gallery access
- Review notification settings - Prevent message previews on lock screens
- Disable social media linking - Prevent cross-platform data sharing
- Enable two-factor authentication - Add extra account security layers
- Configure profile visibility - Control who can discover your profile
- Review data sharing preferences - Limit third-party data access
What Information Should You Never Share on Dating Profiles?
Information security on dating platforms requires careful consideration of what personal details to include versus those that should remain private until trust is established. Certain categories of information pose immediate security risks when included in public profiles or early conversations.
Financial information, including specific job titles, company names, or income details, can attract financial predators or enable social engineering attacks. While discussing salary transparency in dating has become more common, detailed financial disclosure should occur only after establishing genuine connection and trust.
Home addresses, specific neighborhood details, routine schedules, or frequent location check-ins create vulnerability patterns that malicious actors can exploit for stalking or harassment. Children's information, including names, schools, or custody arrangements, should never appear in dating profiles due to safety and legal implications.
| Information Category | Risk Level | Safe Alternative |
|---|---|---|
| Full Legal Name | High | First name or nickname only |
| Home Address | Critical | General area or city |
| Workplace Details | High | Industry or profession type |
| Phone Number | Medium | Use in-app messaging initially |
| Social Media Handles | Medium | Share after establishing trust |
| Financial Information | High | General lifestyle indicators |
| Children's Details | Critical | Mention parenthood without specifics |
| Daily Schedule | High | General availability preferences |
How Can You Recognize and Avoid Romance Scams?
Romance scams have become increasingly sophisticated, employing psychological manipulation techniques combined with advanced technology to create convincing fraudulent relationships. Modern scammers often use stolen photos, fabricated life stories, and even AI-generated content to maintain deceptive personas over extended periods.
Red flag indicators include rapid emotional escalation, reluctance to meet in person or video chat, requests for financial assistance, and inconsistent personal details. Professional scammers often claim military deployment, international business travel, or family emergencies to explain their unavailability for face-to-face meetings.
Sophisticated operations may involve multiple team members maintaining single fake profiles, ensuring consistent communication patterns and detailed backstory maintenance. Some scams incorporate weaponized vulnerability techniques to accelerate emotional attachment and reduce critical thinking about inconsistencies.
Romance Scam Warning Signs
- Excessive early affection - Love declarations within days
- Avoidance of real-time communication - No phone or video calls
- Professional-quality photos - Images that seem too perfect
- Vague personal details - Inconsistent or limited background information
- Financial requests - Any money-related appeals or emergencies
- Grammar inconsistencies - Language patterns suggesting non-native speakers
- Rushed relationship progression - Pressure to move off-platform quickly
- Limited social media presence - Minimal or recently created accounts
What Are the Best Secure Messaging Practices for Online Dating?
Secure communication forms the foundation of safe online dating interactions, requiring careful attention to message content, platform selection, and information sharing progression. Begin relationships using dating app messaging systems rather than immediately transitioning to personal communication channels.
Most reputable dating platforms implement content monitoring systems that can detect and flag suspicious behavior, providing an additional security layer during initial interactions. Personal phone numbers, email addresses, or social media accounts should only be shared after establishing genuine connection and trust through multiple conversations.
When transitioning to external messaging platforms, prioritize applications offering end-to-end encryption, such as Signal or WhatsApp, over standard SMS or less secure messaging services. Be aware that conversation fatigue can reduce vigilance about security practices.
Progressive Information Sharing Strategy
- Phase 1 (Days 1-7): Use only in-app messaging, share general interests
- Phase 2 (Week 2): Consider voice calls through secure apps, share more personal preferences
- Phase 3 (Week 3-4): Video calls to verify identity, exchange limited social media
- Phase 4 (Month 2+): Share contact information after establishing trust and meeting in person
How Should You Handle Photo Privacy and Image Security?
Image security on dating platforms presents unique challenges, as photos serve as primary attraction tools while simultaneously creating significant privacy vulnerabilities. Reverse image searches enable bad actors to discover additional social media profiles, personal information, or even professional details through photo recognition technology.
Metadata embedded in digital photos can reveal precise location coordinates, camera equipment details, and timestamps that provide insights into personal routines and behaviors. Modern smartphones automatically include GPS coordinates in image files unless specifically disabled through camera settings.
Consider using dating-specific photos that don't appear on other social media platforms to prevent easy cross-referencing. Professional or semi-professional photos, while attractive, may appear in multiple online contexts that could compromise anonymity. Understanding profile psychology and potential manipulation can also inform photo selection strategies.
Photo Security Best Practices
- Remove metadata before uploading photos to dating apps
- Use unique images that don't appear on social media
- Avoid identifiable backgrounds like home addresses or workplace locations
- Disable location services in camera settings
- Consider photo editing to slightly alter identifying features
- Limit personal item visibility such as name tags or distinctive belongings
- Use recent photos to maintain authenticity while ensuring current appearance
- Avoid group photos that could compromise friends' privacy
Which Dating Apps Offer the Strongest Privacy Protection?
Privacy-focused dating applications have emerged in response to growing cybersecurity concerns, implementing enhanced security measures that prioritize user data protection over extensive behavioral tracking. These platforms typically offer features like end-to-end encryption, minimal data collection, and transparent privacy policies.
Signal-based dating apps integrate secure messaging protocols directly into their matching systems, ensuring that conversations remain private from platform operators. Some applications implement zero-knowledge architecture, meaning even the company cannot access user messages or detailed profile information.
However, enhanced privacy often comes with trade-offs in matching algorithm sophistication or user base size. The most privacy-conscious apps may have smaller user pools, potentially limiting connection opportunities but providing significantly better data protection for users prioritizing security over convenience.
Privacy-Focused Dating Platform Features
- End-to-end encryption for all communications
- Minimal data collection policies and transparent terms
- No third-party data sharing or advertising network integration
- Regular security audits and vulnerability assessments
- User data deletion options and account termination procedures
- Anonymous browsing modes and profile privacy controls
- Photo verification systems to reduce catfishing risks
- Location privacy features beyond basic GPS controls
What Should You Do If Your Dating App Account Gets Compromised?
Account compromise incidents require immediate response protocols to minimize potential damage and protect personal information from further exposure. The first critical step involves changing passwords not only for the affected dating app but also for any accounts using similar or identical credentials.
Data breach scenarios may involve unauthorized access to messages, photos, personal information, or financial details if payment information was stored within the application. Contact the dating platform's customer support immediately to report the incident and request account suspension while investigation occurs.
Document all evidence of the compromise, including suspicious messages, unauthorized profile changes, or unusual account activity. This information proves valuable for both platform investigations and potential law enforcement involvement if criminal activity is suspected or financial fraud has occurred.
Account Compromise Response Checklist
- Change passwords immediately for the dating app and related accounts
- Enable two-factor authentication if not already activated
- Contact platform support to report the security incident
- Review recent account activity and document suspicious behavior
- Check financial accounts for unauthorized transactions
- Monitor credit reports for potential identity theft
- Warn recent matches about potential impersonation attempts
- Consider temporary account deactivation until security is restored
How Can You Safely Meet Dating App Matches in Person?
Physical meeting security represents the culmination of online dating safety practices, requiring careful planning and risk assessment before transitioning from digital to in-person interactions. Safe meeting protocols should begin with thorough identity verification through video calls and social media cross-referencing.
Choose public venues for initial meetings, preferably during daylight hours and in locations with good cellular reception and security cameras. Inform trusted friends or family members about meeting plans, including location details, timing, and expected duration. Consider using digital safety practices to maintain security awareness throughout the process.
Transportation independence ensures you maintain control over your ability to leave if situations become uncomfortable or dangerous. Avoid accepting rides from dates or sharing detailed information about your vehicle, parking location, or travel routes to and from meeting venues.
Safe Meeting Protocol
- Meet in public spaces with good lighting and security presence
- Arrange independent transportation to maintain departure flexibility
- Inform trusted contacts about meeting details and expected timeline
- Verify identity beforehand through video calls and social media
- Choose familiar locations where you know surroundings and exits
- Limit alcohol consumption to maintain alertness and judgment
- Trust instincts and leave immediately if feeling uncomfortable
- Keep phone charged and maintain emergency contact accessibility
Advanced Privacy Protection Strategies for Serious Daters
Advanced users seeking maximum privacy protection while maintaining active dating lives can implement sophisticated security measures that go beyond basic app settings and standard safety practices. These strategies require additional effort but provide significantly enhanced protection against various cyber threats.
Virtual Private Networks (VPNs) can mask your actual location and IP address when using dating apps, preventing location-based tracking and reducing targeted advertising based on geographic data. Consider using dedicated devices or browser profiles exclusively for dating activities to compartmentalize personal information exposure.
Create separate email addresses specifically for dating platform registrations, using services that prioritize privacy and don't require personal information for account creation. This approach limits cross-contamination between dating activities and other online presence while providing better control over data compartmentalization.
"Privacy is not about hiding something wrong; it's about protecting something important. In dating, that 'something' is your personal security, emotional well-being, and the freedom to explore relationships on your own terms without fear of exploitation or harassment."
Regular privacy audits of your dating app activities help identify potential vulnerabilities or information leakage over time. Review profile information, message histories, and shared photos periodically to ensure they still align with your privacy standards and security comfort level.
Conclusion
Cybersecurity dating app privacy requires ongoing vigilance and systematic implementation of protective measures across multiple security layers. From initial profile creation to in-person meetings, each stage of the online dating process presents unique risks and opportunities for better protection. Understanding data collection practices, implementing robust privacy settings, and maintaining healthy skepticism about potential threats creates a foundation for safer digital romance. Remember that effective privacy protection doesn't require sacrificing authentic connections—it simply means being smart about how you share personal information and with whom you choose to share it. As dating technology continues evolving, staying informed about emerging threats and new protective tools ensures your romantic pursuits remain both exciting and secure in 2026 and beyond.